Fundamentals of Cyber Security: A Comprehensive Guide
Learn the core principles of cybersecurity, including the CIA Triad, common digital threats, cryptography basics, and essential security best practices.
FUNDAMENTALS OF<br>CYBER SECURITY
Protecting the Digital World
Cybersecurity Essentials
WHAT IS<br>CYBER SECURITY?
Cyber Security is the practice of protecting systems, networks, and programs from digital attacks, unauthorized access, damage, or data theft.
Safeguarding digital infrastructure
Preventing unauthorized access
Ensuring data confidentiality & integrity
The CIA Triad
The Foundation of Information Security
CONFIDENTIALITY
Ensuring information is accessible only to authorized users
INTEGRITY
Maintaining accuracy and completeness of data
AVAILABILITY
Ensuring systems and data are accessible when needed
TYPES OF CYBER THREATS
Malware
Malicious software designed to damage systems
Phishing
Deceptive attempts to steal sensitive info
Ransomware
Encrypts data and demands payment
DDoS Attack
Overwhelms servers with traffic
Man-in-the-Middle
Intercepts communication between parties
SQL Injection
Inserts malicious SQL code into databases
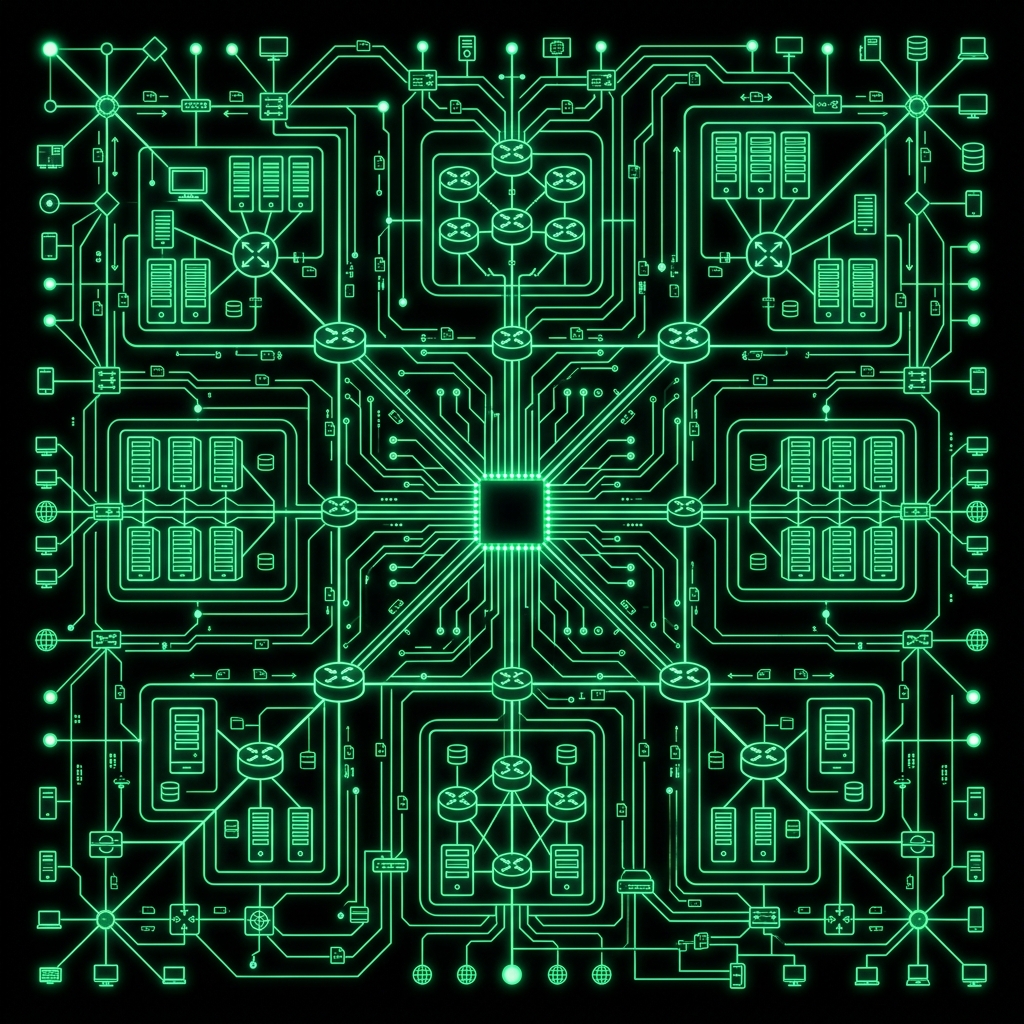
Network Security
Protecting your network infrastructure
Firewalls
Filter incoming/outgoing traffic
VPN
Encrypts internet connections
Intrusion Detection Systems (IDS)
Network Segmentation
Cryptography Basics
Securing Data Through Encryption
Symmetric Encryption
Uses the same key for both encryption and decryption of data. Fast and efficient for large blocks of data.
AES
DES
Asymmetric Encryption
Utilizes paired public and private keys. High security, ideal for secure data exchanges over the internet.
RSA
ECC
Hashing
A one-way transformation converting variable-size data into a fixed-length unique signature or fingerprint.
SHA-256
MD5
Digital Signatures
Cryptographic mechanism used to verify the authenticity, integrity, and non-repudiation of digital documents.
Authenticity
Integrity
AUTHENTICATION & ACCESS CONTROL
Verifying Identity & Managing Permissions
01. Authentication Methods
Passwords
Biometrics
Multi-Factor Authentication (MFA)
Smart Cards
02. Authorization
Role-Based Access Control (RBAC)
Least Privilege Principle
03. Identity Management
Single Sign-On (SSO)
Directory Services
Common Cyber Attack Lifecycle
How Attackers Operate
Security Best Practices
Staying Protected in the Digital Age
Use Strong Passwords & MFA
Keep Software Updated
Regular Data Backups
Use Firewalls & Antivirus
Encrypt Sensitive Data
Employee Security Training
Monitor Network Activity
Zero Trust Architecture
Key Takeaways
<strong style="color: #00ff41; font-weight: 600;">Cyber Security</strong> protects systems, networks, and data from threats
<strong style="color: #00ff41; font-weight: 600;">The CIA Triad</strong> — Confidentiality, Integrity, Availability — is the foundation
<strong style="color: #00ff41; font-weight: 600;">Threats include</strong> malware, phishing, ransomware, and more
<strong style="color: #00ff41; font-weight: 600;">Cryptography and authentication</strong> are critical defenses
<strong style="color: #00ff41; font-weight: 600;">Security is an ongoing process</strong>, not a one-time fix
Stay Secure. Stay Vigilant.
- cybersecurity
- information-security
- cia-triad
- networking
- cryptography
- malware-prevention
- it-security