OCR A Level Computer Science Paper 1: CPU & System Revision
Master OCR A Level Computer Science Paper 1 topics: Von Neumann architecture, FDE cycle, RISC vs CISC, memory management, and TCP/IP protocol stack.
OCR A Level Computer Science
Paper 1: Computer Systems – Intensive Revision
Exam Focus: CPU Architecture, Memory, Networks, & Data Structure
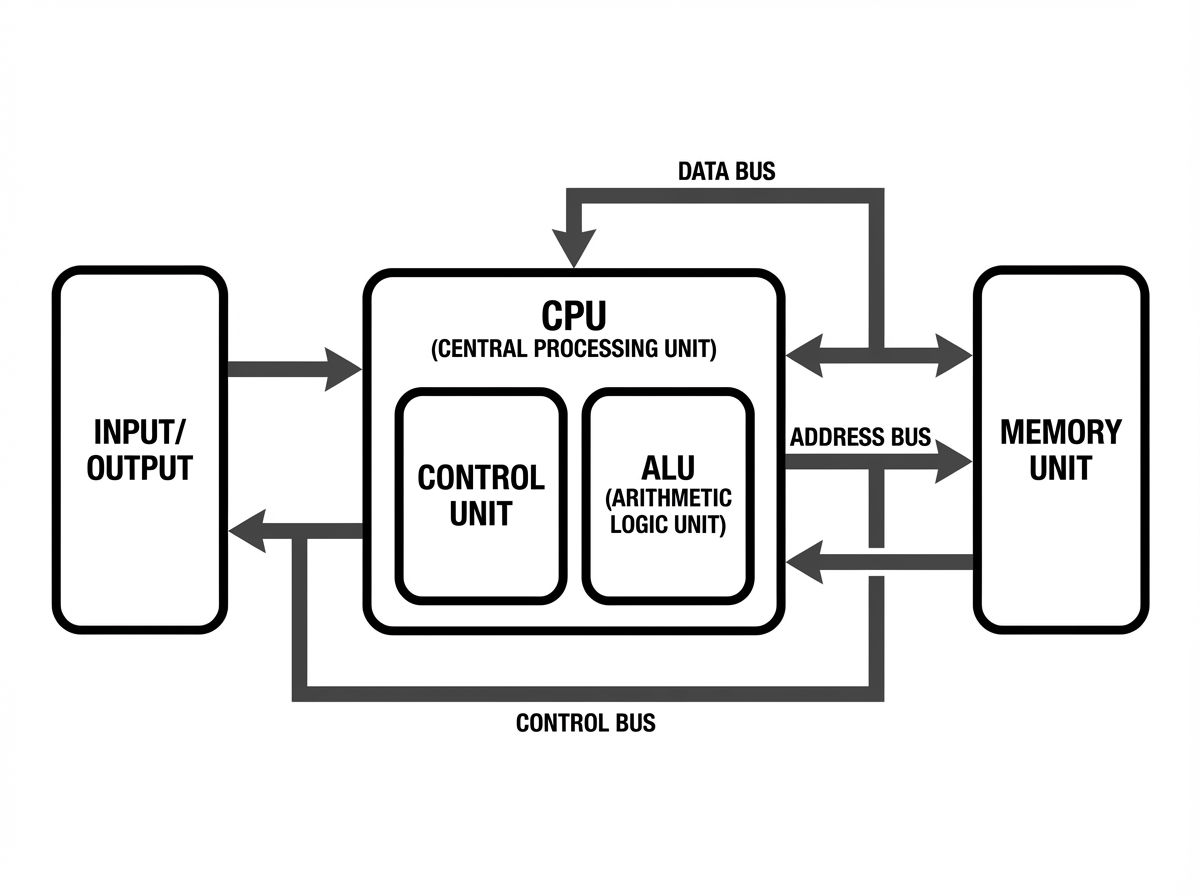
CPU Architecture: Von Neumann Model
Shared Memory: Data and Instructions are stored in the same main memory address space.
Shared Bus: Uses a single set of buses (data & address) for transfer.
Bottleneck: The 'Von Neumann Bottleneck' occurs because instructions and data cannot be fetched simultaneously.
Essential CPU Registers
Program Counter (PC): Holds the address of the next instruction to be executed.
Memory Address Register (MAR): Holds the address of the current instruction/data to be fetched.
Memory Data Register (MDR): Acts as a buffer, holding the actual data or instruction fetched from memory.
Current Instruction Register (CIR): Holds the current instruction being decoded and executed.
Accumulator (ACC): Variable holding the result of arithmetic and logic operations.
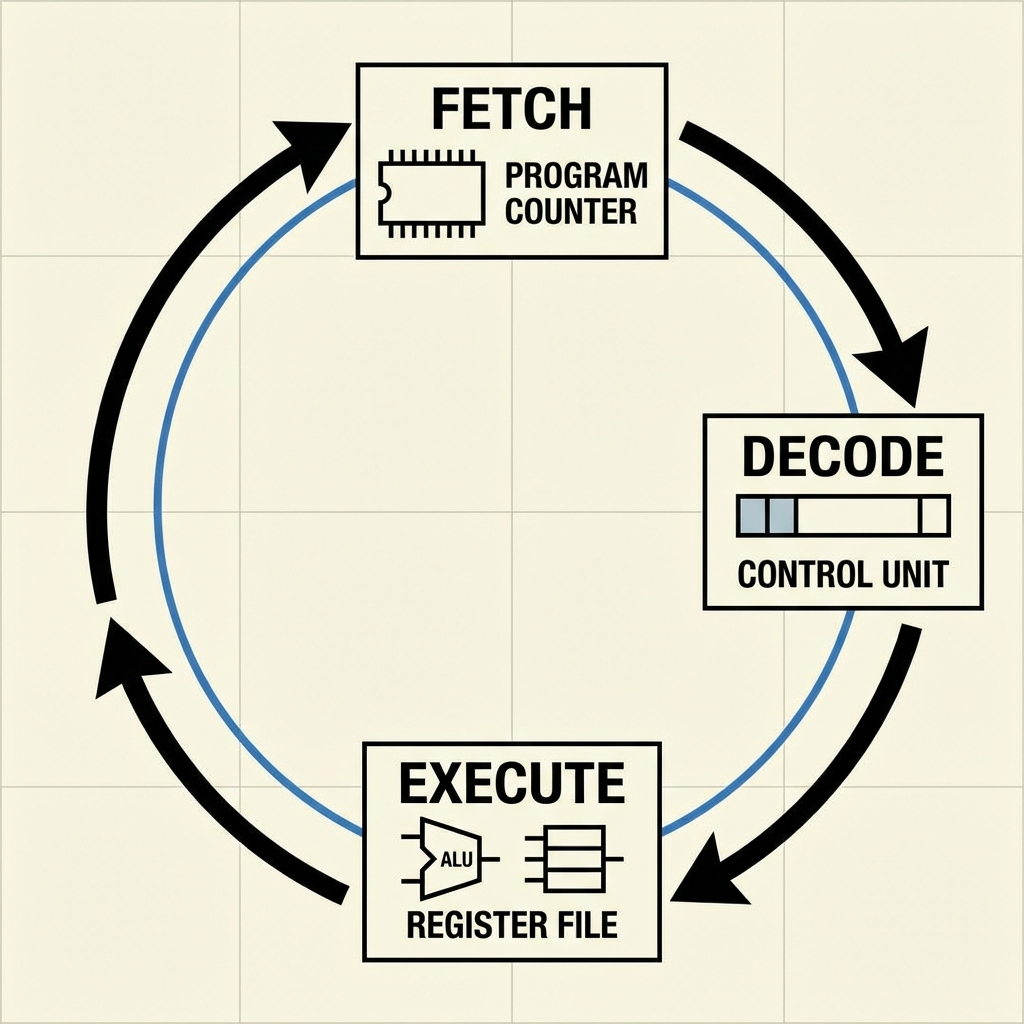
Fetch-Decode-Execute Cycle
FETCH: Address from PC copied to MAR. Instruction found at address in Main Memory copied to MDR. PC incremented by 1. Contents of MDR copied to CIR.
DECODE: Control Unit (CU) interprets the instruction inside the CIR. The opcode is identified.
EXECUTE: The instruction is carried out. This may involve the ALU (calculations), reading/writing to memory, or changing the PC (jumps).
CPU Performance Factors
Clock Speed: Cycles per second (GHz). Higher is generally faster but creates more heat. Number of Cores: Allows parallel execution, though software must be optimized (multithreading). Cache Size: Reduces time waiting for data from main RAM.
CISC vs RISC Architectures
Complex Instruction Set Computer (CISC)<br><br>• Many complex instructions<br>• Hardware is complex<br>• Instructions take multiple cycles<br>• Code is shorter (less RAM used)<br>• Example: x86 (Intel/AMD)
Reduced Instruction Set Computer (RISC)<br><br>• Few simple instructions<br>• Hardware is simpler<br>• Instructions take 1 cycle<br>• Code is longer (more RAM used)<br>• Pipelining is easier<br>• Example: ARM (Mobile devices)
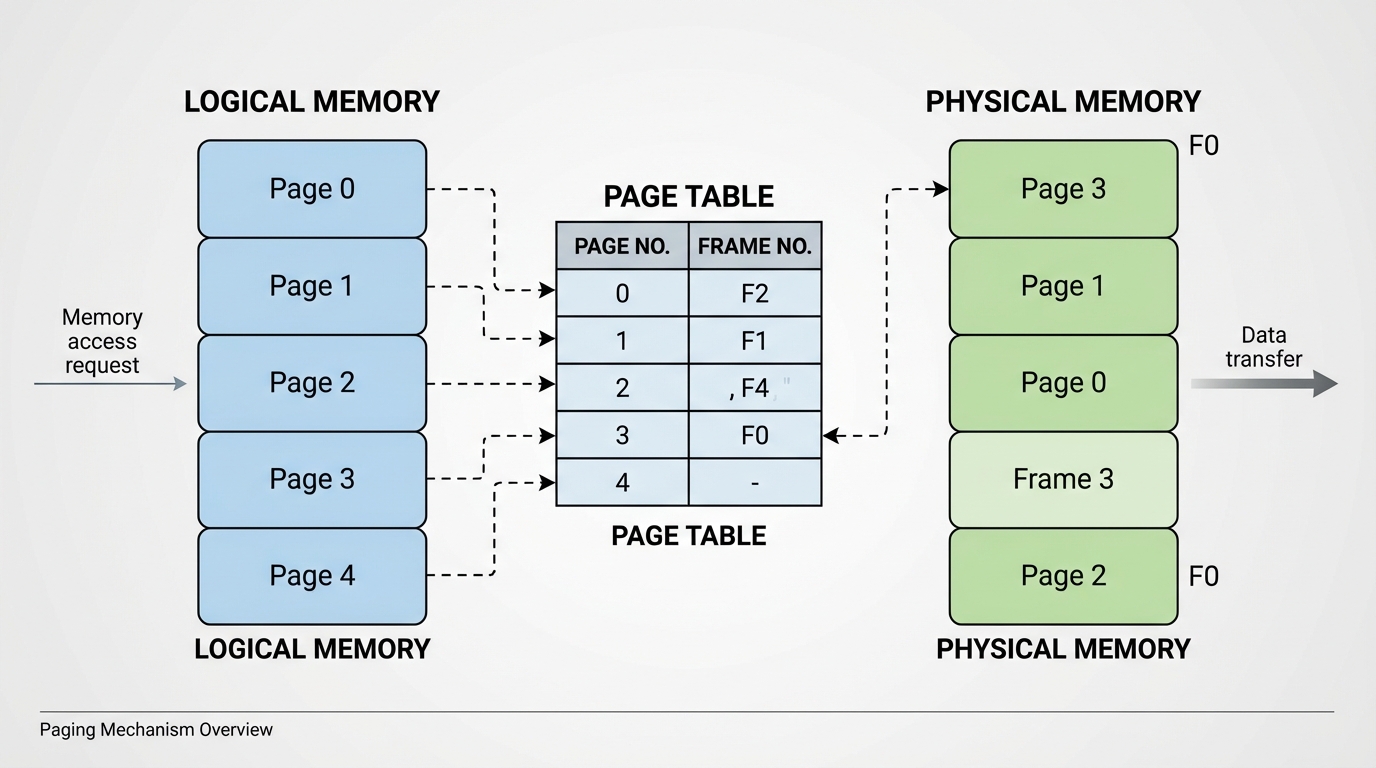
OS Memory Management
Paging: Memory differs into fixed-size physical divisions called page frames. Programs are split into logical pages of equal size. Allows non-contiguous storage.
Segmentation: Memory is divided into variable-sized chunks (segments) based on logical parts of the code (e.g., stack, data, code).
Virtual Memory: Swapping inactive pages to secondary storage (disk) to extend available RAM. Causes 'Thrashing' if overused.
Relational Databases & Normalization
Relational Model: Data stored in tables (relations) linked by keys.<br><br><b>Primary Key:</b> Unique identifier for an entity.<br><b>Foreign Key:</b> Attribute linking to another table's primary key.
<b>1NF:</b> Atomic values, no repeating groups.<br><b>2NF:</b> In 1NF + no partial dependencies.<br><b>3NF:</b> In 2NF + no transitive dependencies (All attributes depend primarily on the Key).
SELECT name, course_id FROM Students WHERE grade = 'A' ORDER BY name ASC;
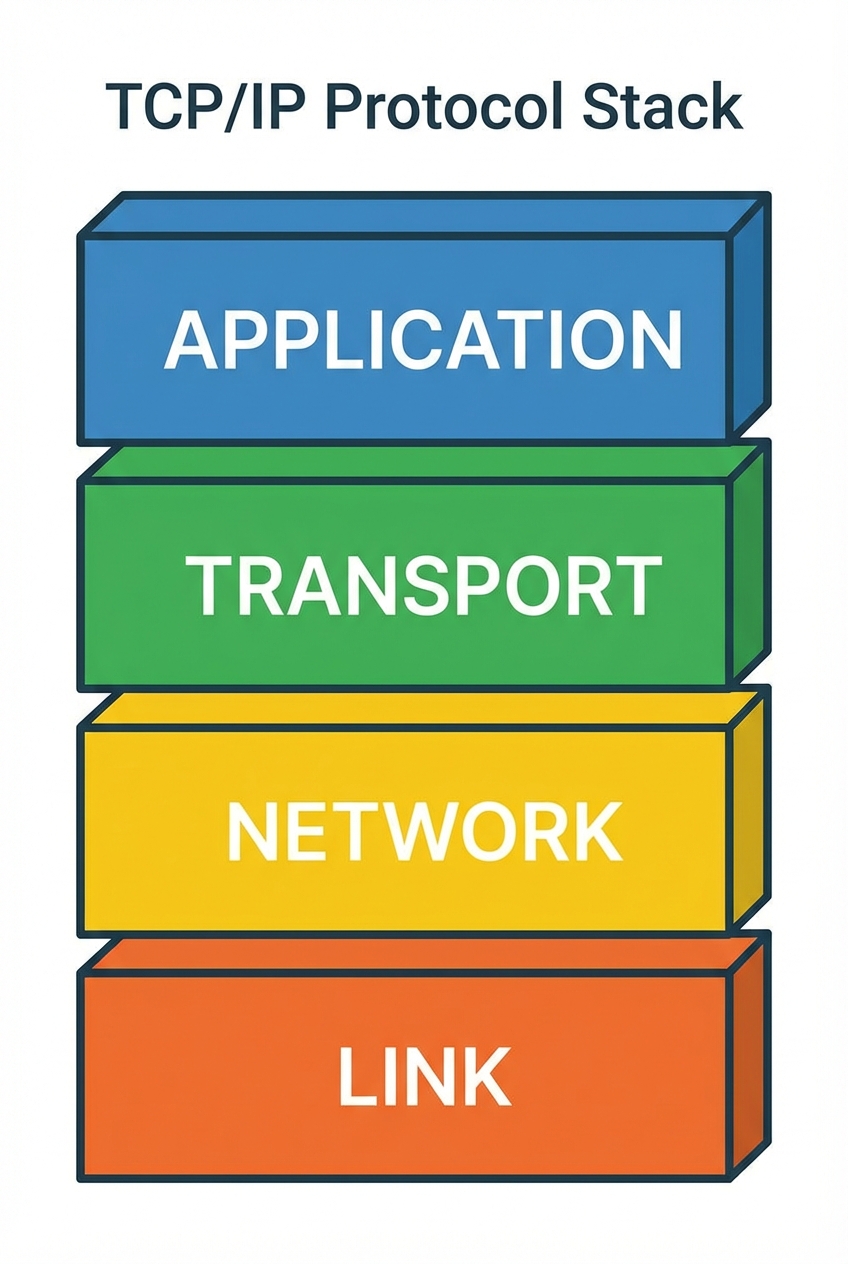
TCP/IP Protocol Stack
Application Layer: HTTP, SMTP, FTP. formatting and presentation of data.
Transport Layer: TCP/UDP. Splits data into packets, error checking, sequencing.
Network Layer: IP. Routing packets across networks (Addressing).
Link Layer: Ethernet/WiFi. Physical transmission (MAC addresses).
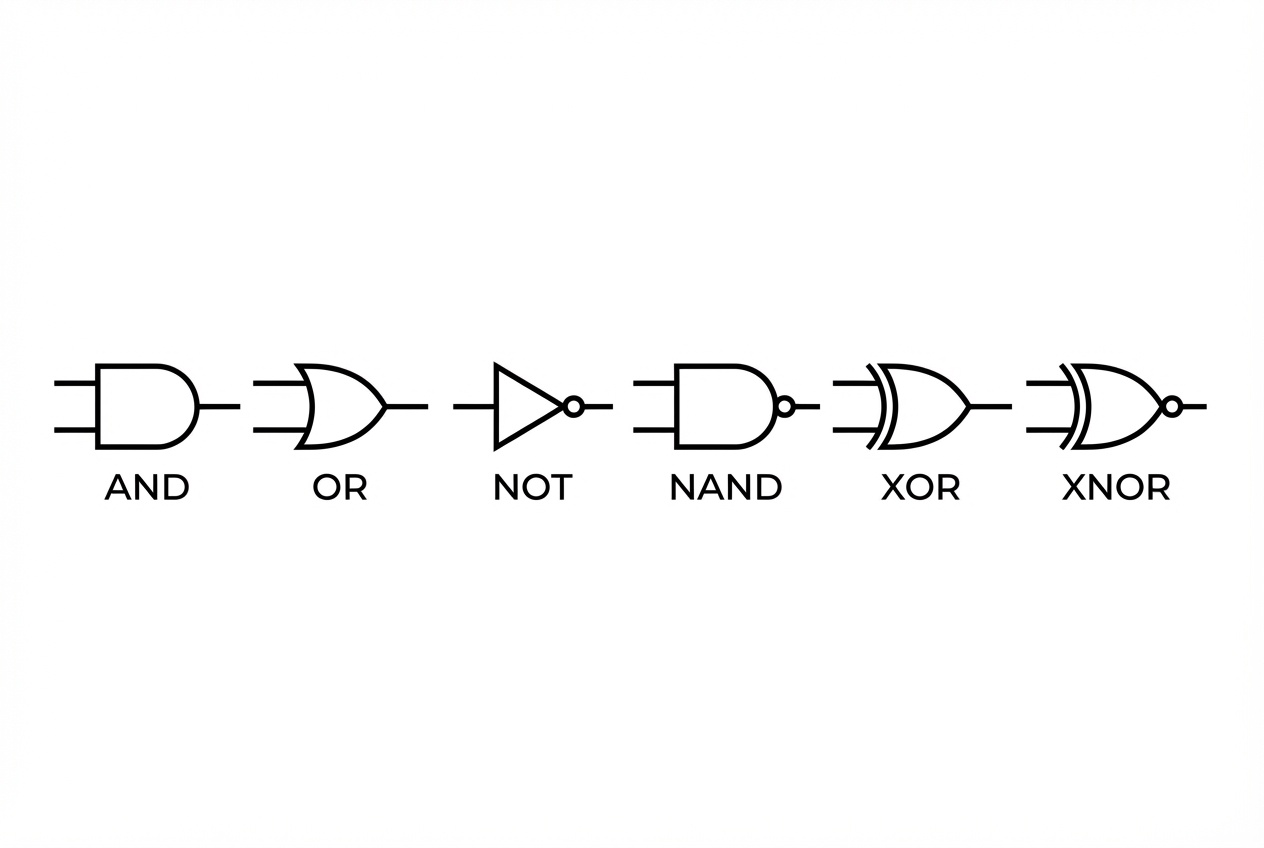
Boolean Algebra & Logic
De Morgan's Laws
¬(A ∧ B) = ¬A ∨ ¬B (NOT(A AND B) = NOT A OR NOT B)
¬(A ∨ B) = ¬A ∧ ¬B (NOT(A OR B) = NOT A AND NOT B)
Karnaugh Maps (K-Maps) are used to simplify Boolean expressions by grouping 1s in powers of 2 (1, 2, 4, 8).
Binary Representation: Floating Point
Floating point numbers are stored as a Mantissa and an Exponent. Structure (Example 8-bit): [Mantissa (Sign bit + value)] [Exponent (Two's Complement)] Normalization: Ensures precision is maximized and numbers have a unique representation. A normalized positive number starts 01... A normalized negative number starts 10...
EXAMPLE: 5.75 Binary: 101.11 Normalized: 0.10111 x 2^3 Mantissa: 01011100 Exponent (3): 0011
Practice Exam Question (Paper 1)
Q: A processor uses the Von Neumann architecture. Explain how the Fetch-Decode-Execute cycle involves the registers when reading an instruction from memory. (6 Marks)
POINTS TO INCLUDE: 1. PC holds address of next instruction. 2. PC content copied to MAR. 3. Address bus used to transfer address to Memory. 4. Control Unit sends Read signal. 5. Content at address sent via Data Bus to MDR. 6. MDR content copied to CIR. 7. PC incremented.
- ocr-a-level
- computer-science
- cpu-architecture
- fetch-decode-execute
- risc-cisc
- networking
- revision-guide