E-Commerce Threat Modeling & STRIDE Security Architecture
Learn how to apply the STRIDE framework to secure e-commerce platforms, including risk assessment, security controls, and architectural mitigation.
Threat Modeling and Security Architecture
Project 2: Implementation of STRIDE for E-Commerce
Prepared by: Aryan Kumar Singh<br>Amity University Online | Course: IHC - PACS<br>Project Given By: TCS iON
Introduction & Objectives
<strong>Objective:</strong> Apply STRIDE threat modeling to a real-world e-commerce application to identify security gaps.
<strong>Methodology:</strong> Identify threats (Spoofing, Tampering, etc.) and design a secure architecture.
<strong>Importance:</strong> E-commerce sites handle sensitive financial data and are frequent targets for cyberattacks.
<strong>Goal:</strong> Reduce security risks through early identification and architectural mitigation.
Application Overview: E-Commerce
<strong>System Description:</strong><br>An online retail platform allowing users to browse products, register, login, and execute secure payments.<br><br><strong>Key Components:</strong><br><ul><li>Web Frontend (User Interface)</li><li>Application Server (Business Logic)</li><li>Database (User & Order Data)</li><li>Payment Gateway Integration</li><li>Admin Panel for Management</li></ul>
Threat Modeling Methodology: STRIDE
<strong>S</strong>poofing: Impersonating something or someone else.
<strong>T</strong>ampering: Modifying code or data without authorization.
<strong>R</strong>epudiation: Denying responsibility for an action.
<strong>I</strong>nformation Disclosure: Exposing confidential data.
<strong>D</strong>enial of Service: Denying access to valid users.
<strong>E</strong>levation of Privilege: Gaining unauthorized access levels.
Identified Threats in E-Commerce
<div style='display: flex; flex-wrap: wrap; gap: 20px; justify-content: center;'><div style='width: 45%; background: #fff0f0; padding: 20px; border-left: 5px solid #e53e3e;'><strong>Spoofing</strong><br>Attackers creating fake user accounts or impersonating admins to gain entry.</div><div style='width: 45%; background: #fff0f0; padding: 20px; border-left: 5px solid #e53e3e;'><strong>Tampering</strong><br>Manipulation of order pricing or quantities in transit or at rest in the DB.</div><div style='width: 45%; background: #fff0f0; padding: 20px; border-left: 5px solid #e53e3e;'><strong>Information Disclosure</strong><br>Leakage of customer PII (Personally Identifiable Information) or payment details.</div><div style='width: 45%; background: #fff0f0; padding: 20px; border-left: 5px solid #e53e3e;'><strong>Denial of Service (DoS)</strong><br>Flooding the server with requests to cause downtime and loss of revenue.</div></div>
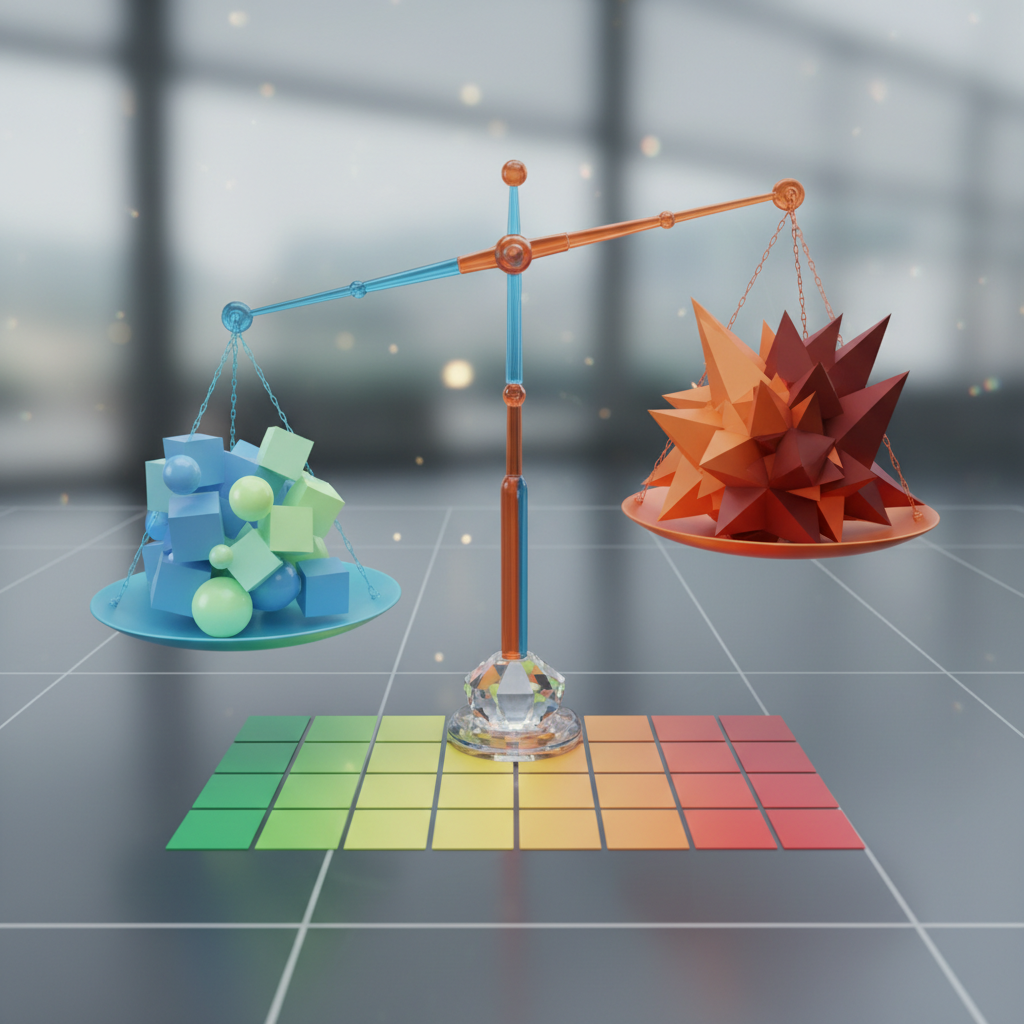
Risk Assessment Methodology
<strong>The Risk Formula:</strong><br><span style='font-size: 2.2rem; color: #2b6cb0;'>Risk = Likelihood × Impact</span><br><br><strong>Evaluation Scope:</strong><br>We analyzed technical vulnerabilities, application logic flaws, and potential business impact.<br><br><strong>Key Factors:</strong><br><ul><li><strong>Likelihood:</strong> Ease of execution for an attacker.</li><li><strong>Impact:</strong> Damage to finances, reputation, or operations.</li></ul>
Risk Assessment Summary
<strong>Critical Risks:</strong><br>Spoofing and Information Disclosure pose the highest threat to the platform, requiring immediate priority in the security architecture.<br><br><strong>High Risks:</strong><br>Data Tampering and Denial of Service can significantly disrupt business operations.
Proposed Security Architecture
<strong>Design Goals:</strong><br>Protect Data, Prevent Access, Ensure Availability.<br><br><strong>Core Components:</strong><ul><li><strong>Frontend:</strong> Secured via HTTPS/TLS 1.3.</li><li><strong>App Layer:</strong> Strict input validation & RBAC (Role-Based Access Control).</li><li><strong>Database:</strong> Encrypted at rest and restricted access.</li><li><strong>Payment:</strong> PCI-DSS compliant gateway integration.</li></ul>
Security Controls & Mitigation
<strong>Technical Controls:</strong><br>Implementation of TLS encryption, strong password hashing (Argon2/Bcrypt), and CSRF tokens.
<strong>Input Validation:</strong><br>Sanitization of all user inputs to prevent SQL Injection and XSS attacks.
<strong>Administrative Controls:</strong><br>Enforcing least-privilege access policies and conducting regular security audits.
<strong>Logging & Monitoring:</strong><br>Real-time logging of login attempts and transaction anomalies.
Advanced Security Measures
<div style='font-size: 1.8rem; line-height: 1.8; color: #2d3748;'><ul style='list-style: none; padding: 0;'> <li style='margin-bottom: 30px; background: #ebf8ff; padding: 20px; border-left: 8px solid #3182ce;'><strong>Web Application Firewall (WAF):</strong><br>Filters and monitors HTTP traffic between chaos and the internet to block common attacks.</li> <li style='margin-bottom: 30px; background: #ebf8ff; padding: 20px; border-left: 8px solid #3182ce;'><strong>Rate Limiting:</strong><br>Restricts the number of requests a user can make in a given timeframe to prevent DoS.</li> <li style='margin-bottom: 30px; background: #ebf8ff; padding: 20px; border-left: 8px solid #3182ce;'><strong>Vulnerability Scanning:</strong><br>Automated tools to detect new security wekanesses in dependencies or configurations.</li> </ul></div>
Implementation Plan
<strong>Phase 1: Foundation</strong><br>Threat identification (STRIDE), basic authentication setup, and HTTPS enforcement.
<strong>Phase 2: Hardening</strong><br>Apply Role-Based Access Control (RBAC), input validation sanitizers, and setup logging mechanisms.
<strong>Phase 3: Advanced Defense</strong><br>Deploy WAF, configure rate limiting, and conduct penetration testing.
A well-designed security architecture combined with threat modeling significantly improves application security.
Key Finding & Conclusion
Reflection Document (1 Page – Content)
<h3 style="color:#2c5282; margin-bottom:25px; font-size: 2rem;">Personal Reflection</h3><p style="margin-bottom:30px;">This project helped me understand how attackers think and how threats can affect real-world applications. Applying the STRIDE framework made threat identification structured and easy to understand.</p><p style="margin-bottom:30px;">The main challenge was mapping theoretical threats to practical application components. This exercise improved my understanding of security architecture and showed how security controls work together to protect systems.</p><p>This assignment strengthened my confidence in threat modeling and security design, which will be useful in future cybersecurity roles.</p>
- threat-modeling
- stride-framework
- cybersecurity
- e-commerce-security
- security-architecture
- risk-assessment