How to Prevent Phishing, Vishing, and Shimming Scams
Learn to identify modern scams including AI voice cloning, smishing, and card shimming. Protect your identity from high-tech fraud and cyber attacks.
Don't Take the Bait: Scam Awareness
Understanding Phishing, Vishing, Shimming & Identity Theft
The Threat Landscape
Phishing
Deceptive emails/texts (Smishing) aimed at stealing logins.
Vishing
Voice fishing: Scammers calling to manipulate you vocally.
Shimming
Physical devices inserted into card readers to steal chip data.
Identity Theft
The result: Using your stolen data to commit fraud.
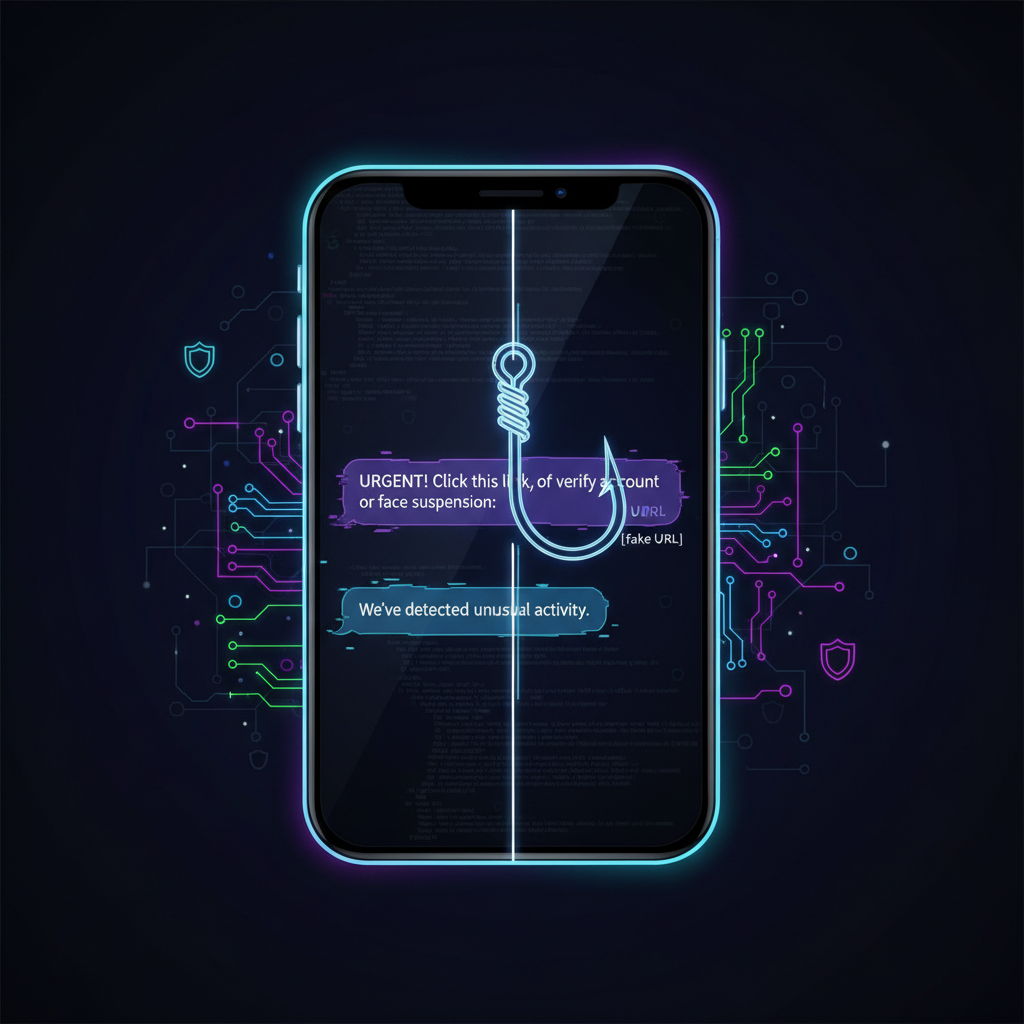
Phishing & Smishing: Digital Bait
Phishing involves fake emails posing as legitimate companies (Netflix, Bank of America, University Admin). When they move to SMS, it's called 'Smishing'.
Creates a sense of urgency ('Account Suspended!')
Uses URL shorteners to hide fake domains
Case Study: The $100 Million Heist
Evaldas Rimasauskas vs. Google & Facebook (2013-2015)
A hacker posed as a hardware supplier (Quanta Computer) using fake email invoices.
Losses: Over $100 Million defrauded from two tech giants.
Outcome: He was caught and extradited, but it proves even tech experts can be fooled.
Vishing & AI Voice Cloning
Attackers now use Artificial Intelligence to clone the voices of family members or CEOs.
Scammers spoof Caller ID to look like 'Local Police' or 'Bank Support'.
Common tactic: 'Grandparent Scam' or 'Kidnapping Scam' using fake audio.
Real Life Vishing: MGM Resorts (2023)
The Scenario
A hacking group called ALPHV found an employee's info on LinkedIn. They called the IT Helpdesk, impersonated the employee, and convinced IT to reset the password.
The Impact
Casinos shut down, slot machines went dark, and room keys stopped working. Estimated cost: $100 Million.
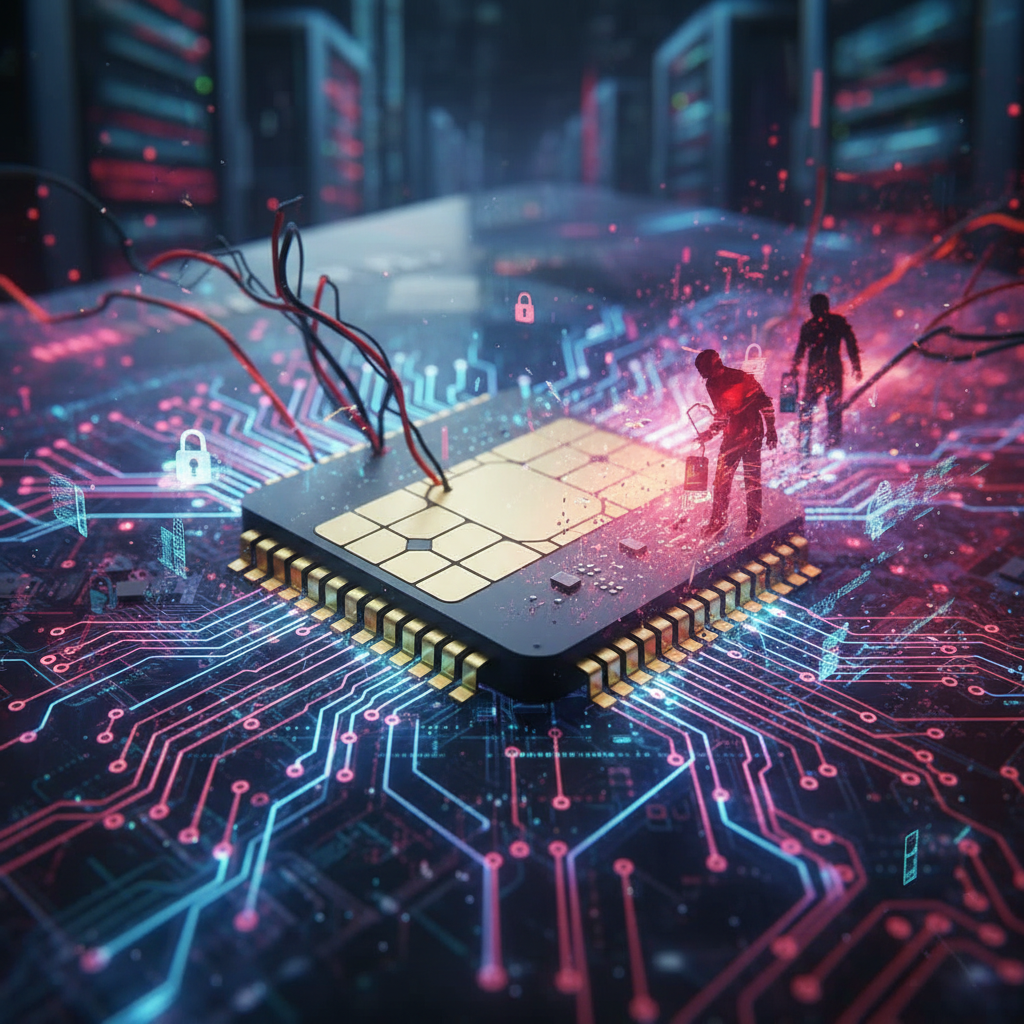
Shimming: The Invisible Card Thief
Unlike bulky 'skimmers' that sit on top of card readers, 'Shims' are paper-thin circuit boards inserted INSIDE the chip reader.
Hard to Detect: They are completely hidden inside the slot.
How it works: It intercepts data between your chip and the bank terminal.
Identity Theft: The Aftermath
What happens when they get your data?
1 in 3
Americans have been victims of identity theft.
New lines of credit opened in your name
Tax return fraud (stealing your refund)
Medical services obtained using your insurance
Daily Scam Frequency (10-Day Sample)
This line graph illustrates an upward trend in reported incidents over a 10-day period, tracking reports of Phishing, Vishing, and Identity Fraud combined.
Identify Threats: Red Flags
Urgency & Threats
"Act Now or be arrested!" - Legitimate orgs don't panic you.
Unknown Payment Methods
Requests for Gift Cards, Crypto, or Wire Transfers.
Context Mismatch
A CEO texting you from a random WhatsApp number.
Don't click. Don't panic. Verify.
If you suspect a scam, contact the entity directly via official channels.
- cybersecurity
- phishing-prevention
- identity-theft
- fraud-awareness
- scam-protection
- vishing
- ai-safety