Visualizing AWS EC2 Network Traffic and Packet Flows
Learn how AWS network traffic flows between public and private subnets, NAT Gateways, and IGWs with this technical architectural visualization.
AWS Network Traffic Simulation
Visualizing Packet Flows: Intra-VPC and Internet Egress
Architecture Topology
Single VPC with split subnets to separate traffic concerns.
Public Subnet: Contains Instance A & B (Web/App Layer). Direct Internet Gateway access.
Private Subnet: Contains Instance C (Backend/DB). Routed through NAT Gateway.
Component Legend & Roles
Flow 1: Same Subnet (A ↔ B)
Direct communication within the Local VPC CIDR. No gateway required. Latency is minimal.
Flow 2: Public to Private (A ↔ C)
Traffic crosses subnet boundaries via the main VPC Router. Instance A connects to Instance C's private IP (e.g., Database access).
Cross-Subnet Animation
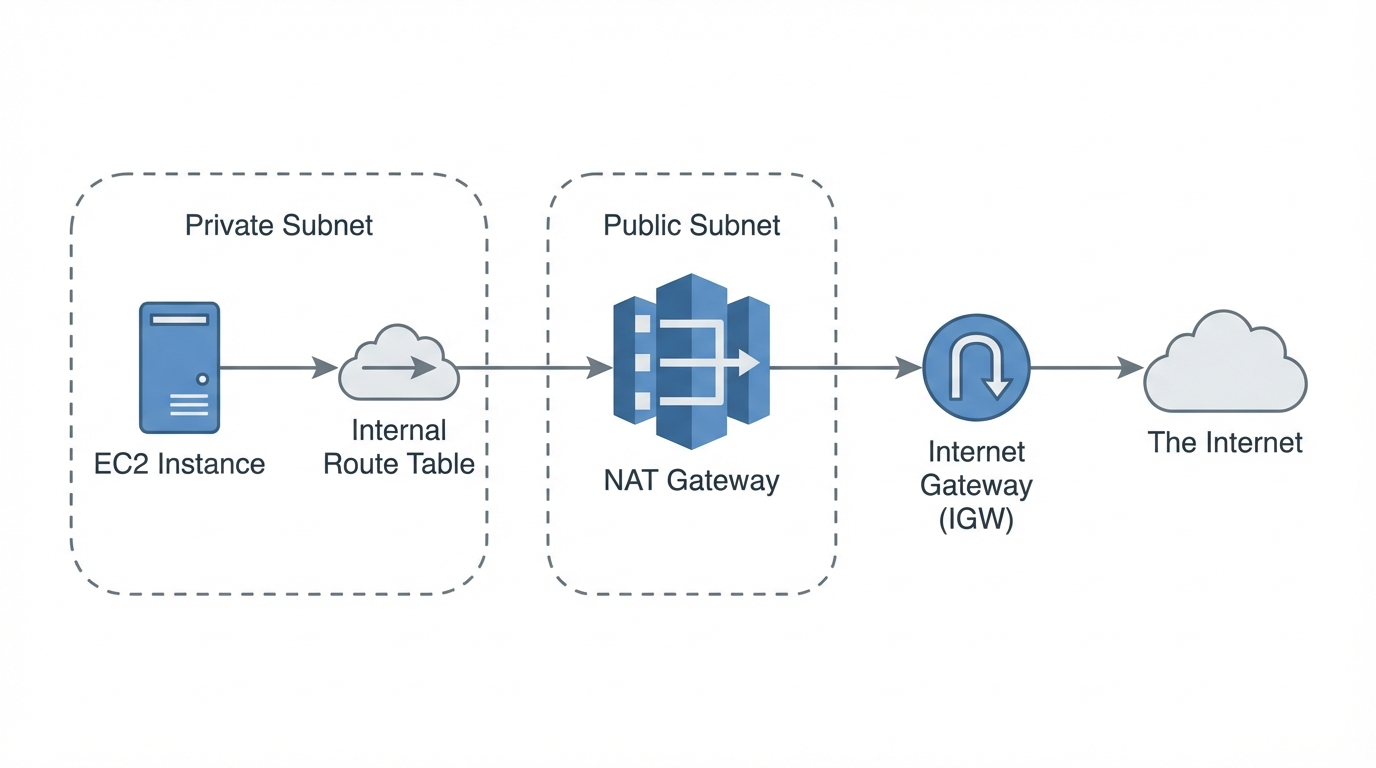
Egress flow: The NAT Gateway
Problem: Private instances have no public IP address.
Solution: Route 0.0.0.0/0 traffic to NAT Gateway in the Public Subnet.
Result: NAT Gateway replaces source IP with its own Elastic IP before hitting the Internet.
Flow 3: Instance C ↔ External Service
Security Controls (Security Groups)
Instance A/B SG: Allow Inbound HTTP (80) from 0.0.0.0/0. outbound All.
Instance C (Private) SG: Allow Inbound only from Instance A/B SG ID.
Summary & Key Takeaways
Internal Communication: Fast, secure, stays within local VPC network.
External Communication: Public instances use IGW; Private instances require NAT.
Security: Use minimal Security Group rules to restrict flow directions.
- aws
- ec2
- vpc
- networking
- nat-gateway
- security-groups
- cloud-architecture
- traffic-flow



 External API
External API