Firmware Encryption Attacks: Mitigating CBC Malleability
Learn how malleability attacks target AES-CBC in encrypted firmware updates and why authenticated encryption (AEAD) is essential for IoT security.
Practical Evaluation of Code Injection in Encrypted Firmware Updates
A critical analysis of malleability attacks on AES-CBC in ARM Microcontrollers
Based on research by O. Guillen, D. Schmidt, & G. Sigl (IEEE, 2016)
The False Sense of Security in Firmware Updates
<ul><li>Many bootloaders rely on symmetric encryption (e.g., AES-CBC) for updates.</li><li><strong>Assumption:</strong> Confidentiality implies security.</li><li><strong>Reality:</strong> Without integrity checks, encrypted data can be manipulated.</li><li><strong>The Threat:</strong> Attacks can inject code <em>without</em> knowing the key.</li></ul>
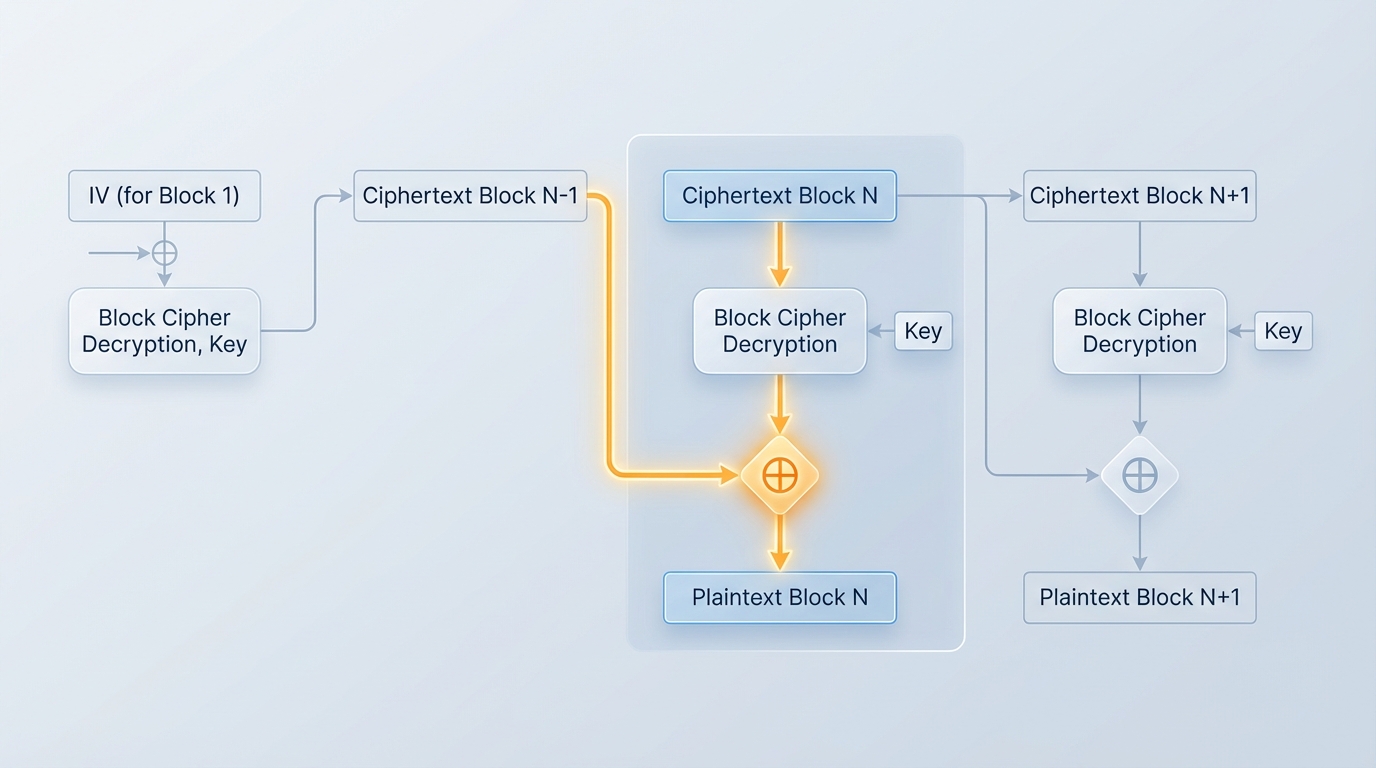
Mechanism of Attack: CBC Malleability
In Cipher Block Chaining (CBC) mode, decryption of a block depends on the previous ciphertext block. Modifying a bit in Ciphertext Block N-1 produces a predictable bit flip in Plaintext Block N.
Targeting the ARM Exception Vector Table (EVT)
To flip bits intelligently, the attacker needs <strong>Known Plaintext</strong>.
On ARM Cortex-M, the EVT is at a fixed location (often 0x00000000).
It contains 'Reserved' vectors that are always initialized to zero.
These 12-20 bytes of known zeros serve as the canvas for code injection.
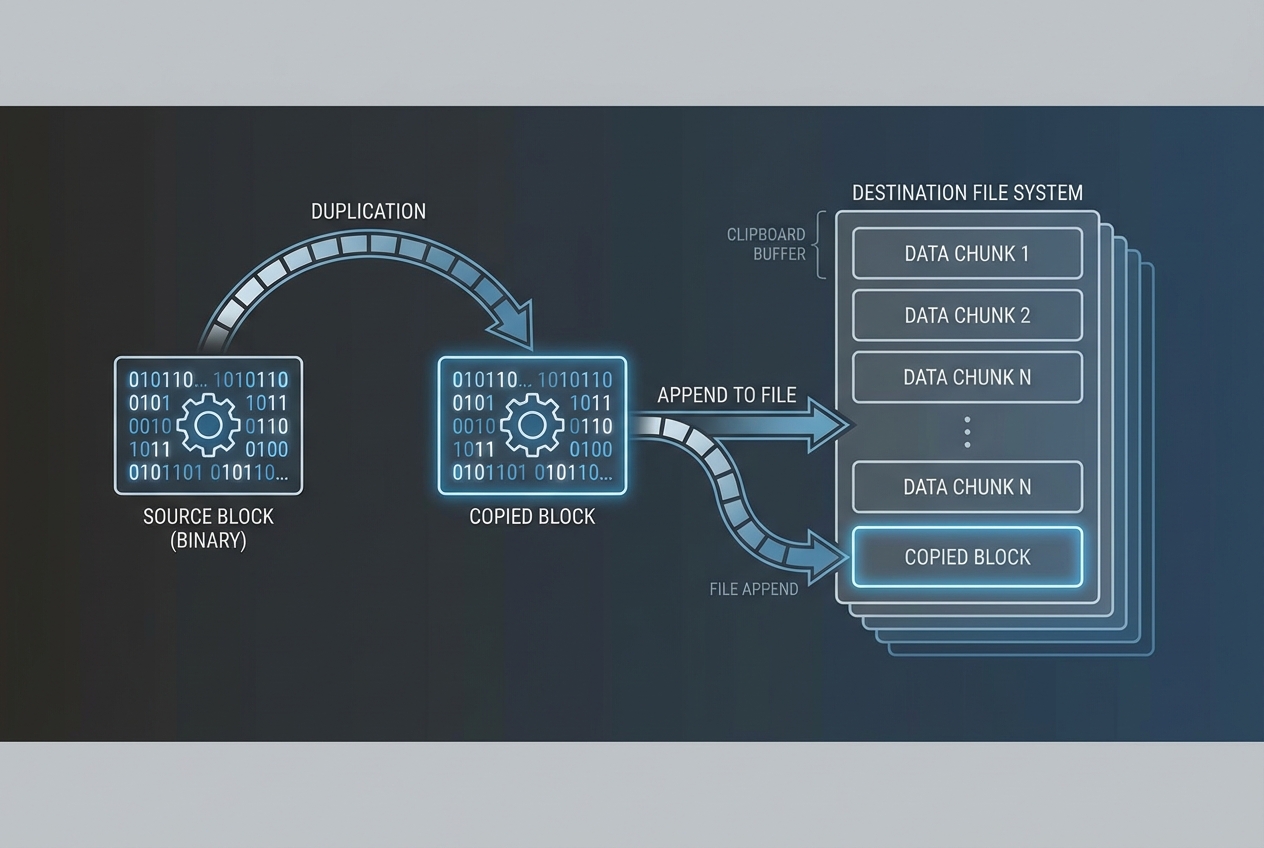
The Copy-and-Paste Attack Strategy
The 'Reserved' EVT space (12 bytes) is too small for a full malicious payload. The attacker uses a 'Copy-and-Paste' technique to expand the available space.
1. Identify the 'Control Block' (Ciphertext N-1) and 'Target Block' (Ciphertext N).
2. Replicate these ciphertext blocks repeatedly at the end of the firmware image.
3. This creates a chain of writable memory sections, interspersed with 'garbage' blocks caused by the decryption corruption.
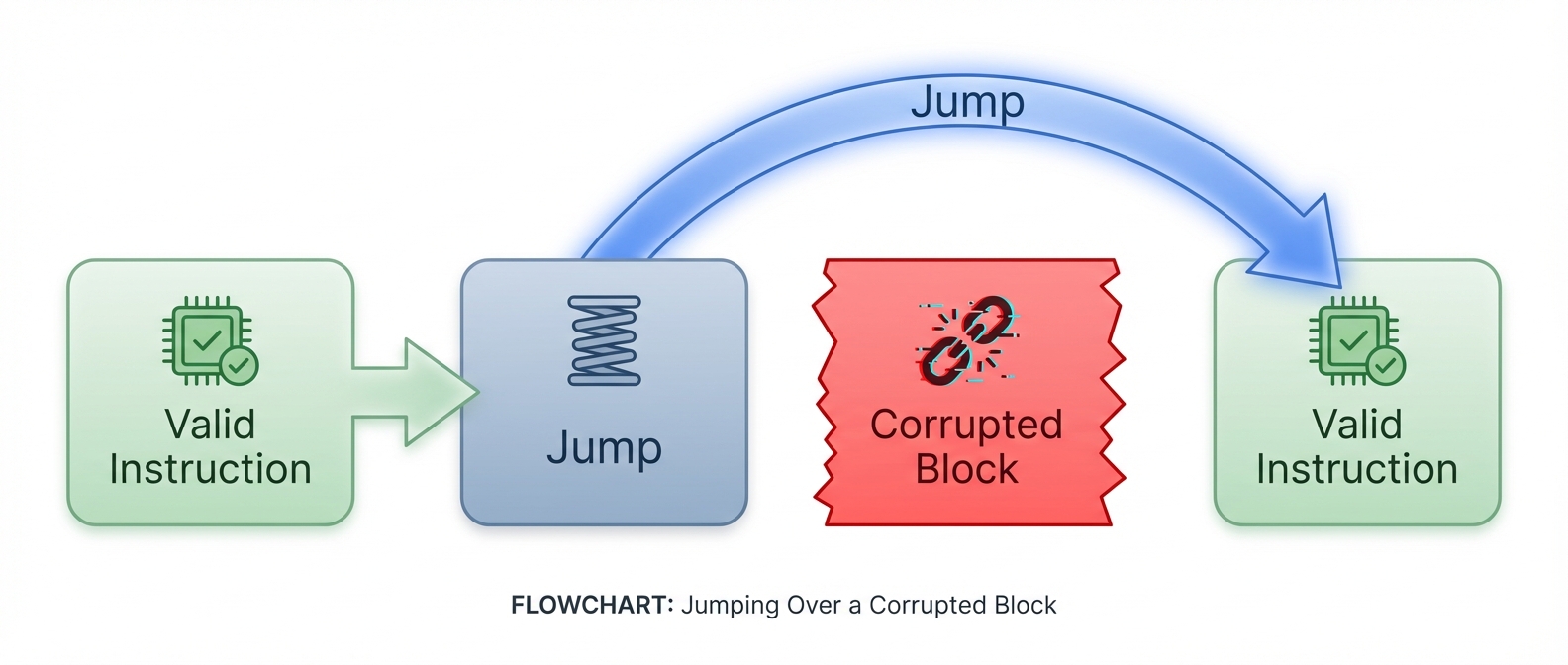
Engineering the Injection: The 'Jump' Technique
When the 'Control Block' is modified to write code into the 'Target Block', the 'Control Block' itself decrypts to random garbage. The code must jump over this corruption.
Triggering Execution
The malicious payload is injected, but the CPU won't run it automatically. To force execution, the attacker modifies the EVT again.
1. Locate the IRQ Vector (e.g., Button Press Interrupt).
2. Bit-flip the vector address to point to the injected code location.
3. Physically interact with the device (press the button) to trigger the jump.
Proof of Concept & Extraction
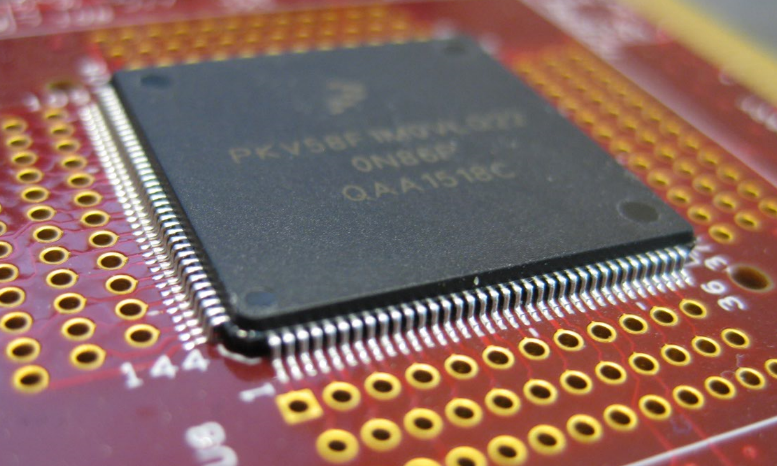
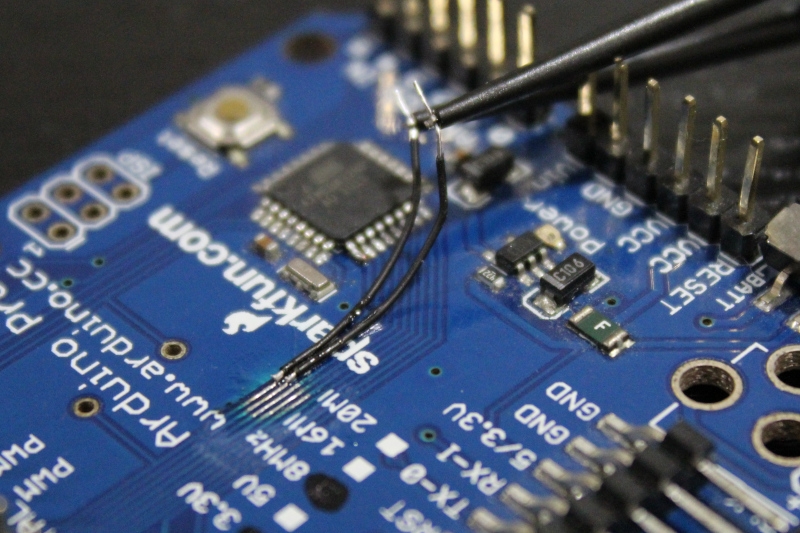
The researchers targeted an Infineon XMC4500 (ARM Cortex-M4). The injected payload acted as a custom SPI transmitter, bit-banging memory contents out via GPIO pins.
<strong>Result:</strong> Full firmware extraction (including secret keys) was achieved using a standard logic analyzer connected to the modified pins.
Mitigation: Authenticated Encryption
Confidentiality fails without Integrity.
<strong>The Solution:</strong> Use Authenticated Encryption with Associated Data (AEAD) modes.
<strong>Examples:</strong> AES-GCM or AES-CCM.
These modes produce an authentication tag. If the ciphertext is modified (malleability attack), the tag verification fails, and the bootloader rejects the update before execution.
Key Takeaways
Encryption (Secrecy) does not guarantee Integrity.
Known plaintext (EVT) allows attackers to break CBC implementations.
Secrets can be extracted without the key by injecting dumper code.
<strong>Always use Authenticated Encryption for Firmware Updates.</strong>
- firmware-security
- aes-cbc-attack
- arm-microcontroller
- embedded-security
- cybersecurity
- code-injection
- aead