Guide to the Social Engineering Toolkit (SET) & Cybersecurity
Learn how the Social Engineering Toolkit (SET) works. Explore spear-phishing, credential harvesting, and effective mitigation strategies for data breaches.
Social Engineering Toolkit
Understanding, Exploiting & Defending Against Human Vulnerabilities
A Comprehensive Overview
Agenda
What is Social Engineering?
What is SET (Social Engineering Toolkit)?
Installation & Setup
Key Features & Modules
Spear-Phishing Attacks
Website Attack Vectors
Credential Harvesting
Live Demo & Screenshots
Defense & Mitigation Strategies
Conclusion & Q&A
What is Social Engineering?
The art of manipulating people into divulging confidential information or performing actions.
Human-Based Attack
Exploits trust and human psychology rather than relying on technological vulnerabilities.
No Code Required
Relies entirely on deception, persuasion, and skilled impersonation techniques.
Primary Threat Vector
Responsible for over 90% of all successful data breaches globally.
Hard to Detect
Effectively bypasses most technical security and access controls.
What is the Social Engineering Toolkit?
SET is an open-source penetration testing framework designed for social engineering attacks. Created by TrustedSec's Dave Kennedy, it is included in Kali Linux and is widely used by ethical hackers and security professionals.
Written in Python
Pre-installed on Kali Linux
Used for authorized penetration testing only
sudo setoolkit
Installation & Setup
Update your system
sudo apt update && sudo apt upgrade
Install SET
sudo apt install set
Launch SET
sudo setoolkit
Select Attack Vector from Menu
1
For authorized use only. Always obtain written permission before testing.
Key Features & Modules
Spear-Phishing Attack Vectors
Targeted email attacks with malicious payloads.
Website Attack Vectors
Clone websites to steal credentials.
Infectious Media Generator
Create autorun exploits on USB drives.
Mass Mailer Attack
Send bulk phishing emails.
Arduino-Based Attack
Microcontroller-based HID attacks.
Powershell Attack Vectors
Windows exploitation via Powershell.
Spear-Phishing Attacks
Crafts targeted emails with embedded malicious files
Supports PDF, DOC, EXE payload formats
Integrates with Metasploit for reverse shell payloads
Can spoof sender email addresses
Works with custom message templates
[ Screenshot: Spear-Phishing Menu ]
SET Spear-Phishing Attack Vector Menu
Website Attack Vectors
Java Applet Attack
Embeds malicious Java on cloned site.
Metasploit Browser Exploit
Exploits browser vulnerabilities.
Credential Harvester
Clones a site and captures login credentials.
Tabnabbing
Replaces inactive browser tab with fake login page.
[ Screenshot: Website Clone Menu ]
SET Website Attack Vectors Menu
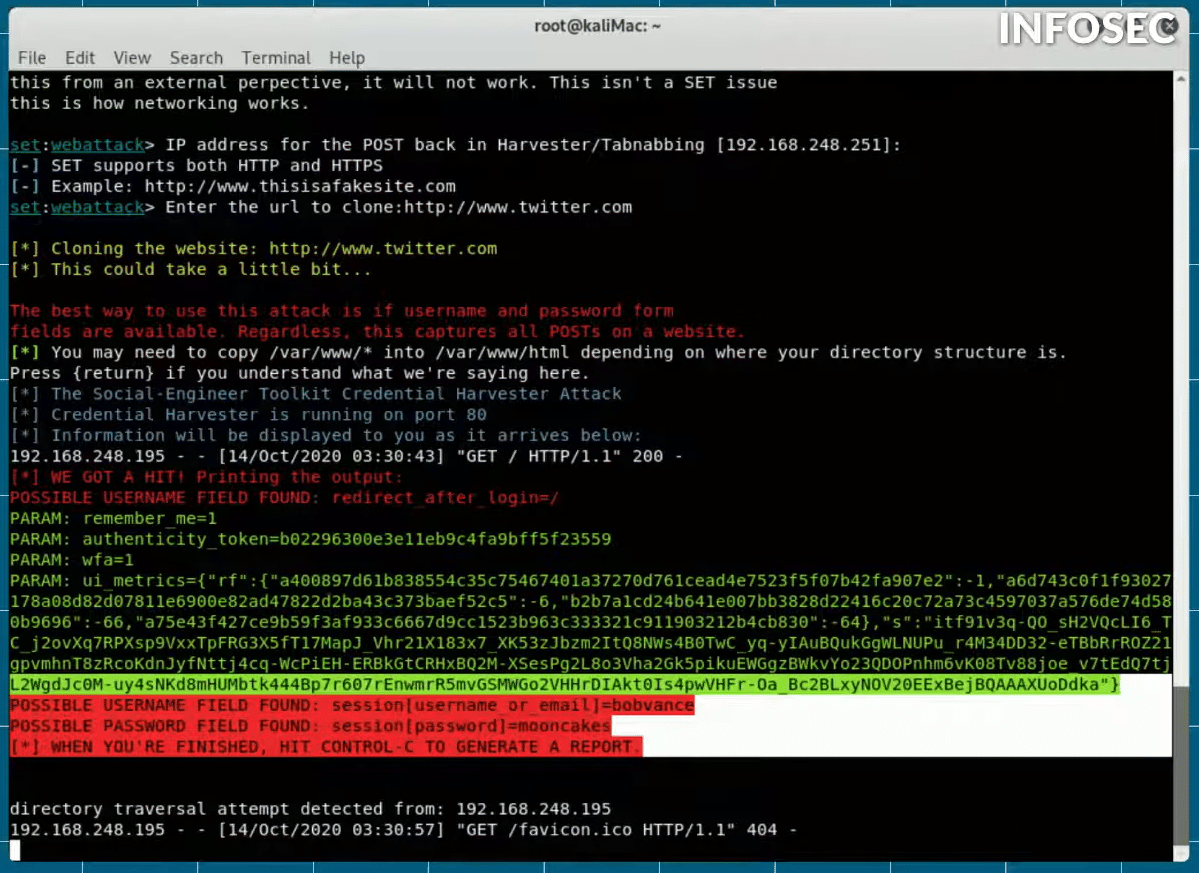
Credential Harvesting
Clone Target Website (e.g., Facebook, Gmail)
Victim Enters Credentials on Fake Page
Credentials Captured & Displayed in Terminal
Supports POST parameter grabbing
Works with any login form
Credentials captured in SET terminal
Live Demo & Screenshots
Real-world SET attack demonstration
[ Screenshot 1 ]
[ Screenshot 2 ]
[ Screenshot 3 ]
[ Screenshot 4 ]
Caption here
Caption here
Caption here
Caption here
Defense & Mitigation Strategies
Security Awareness Training
Educate employees on phishing and social engineering.
Multi-Factor Authentication
Reduce risk of credential theft.
Email Filtering & Anti-Phishing
Block suspicious emails.
Web Filtering
Block access to known malicious domains.
Regular Penetration Testing
Test your own defenses.
Incident Response Plan
Have a plan when an attack occurs.
Thank You
Questions & Discussion
The weakest link in cybersecurity is always the human element.
[ Your Name ] | [ Date ]
- social-engineering
- cybersecurity
- penetration-testing
- phishing-defense
- kali-linux
- network-security
- ethical-hacking